Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Intro to Malware Analysis: What It Is & How It Works - InfoSec

Malware Analysis: Steps & Examples - CrowdStrike
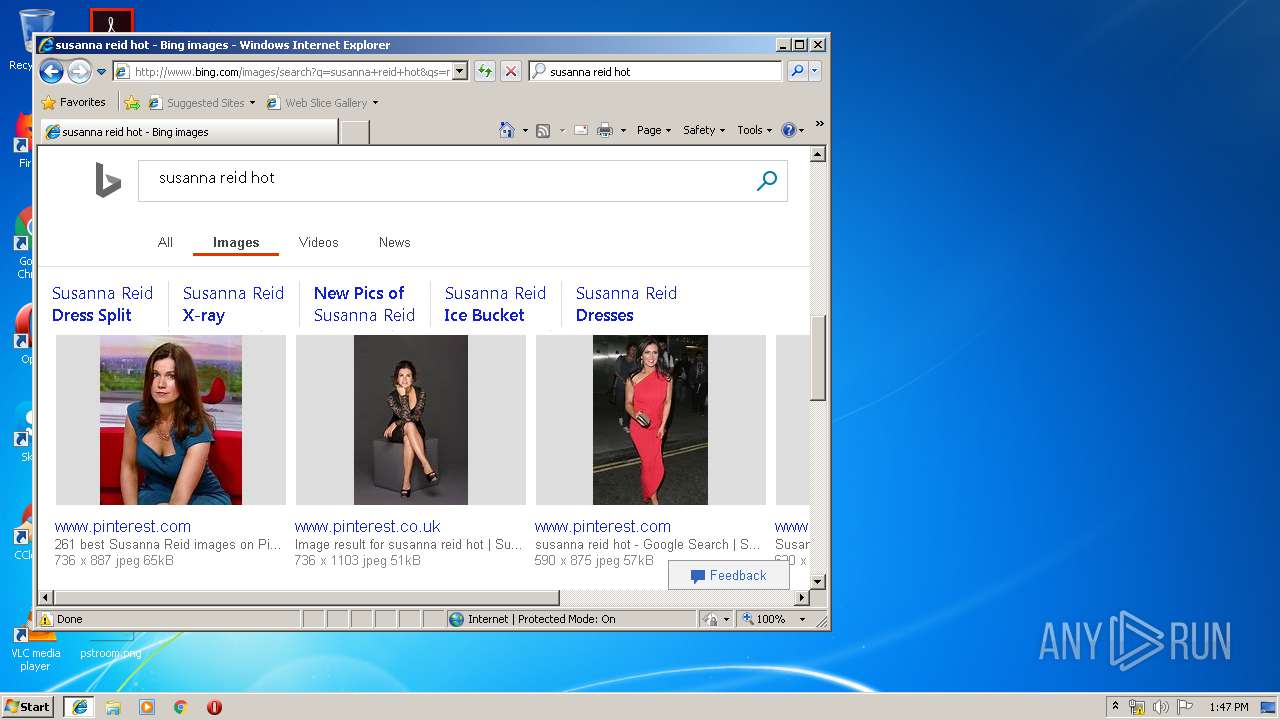
Malware analysis index.html Malicious activity

PROUD-MAL: static analysis-based progressive framework for deep

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging
Malware analysis apksharp.com Malicious activity

Krebs on Security – In-depth security news and investigation

Routers Roasting on an Open Firewall: the KV-botnet Investigation

Malware analysis tt.7z Malicious activity

Malware analysis metasploit.bat Malicious activity

Advanced Automated Malware Analysis – Kaspersky Research Sandbox
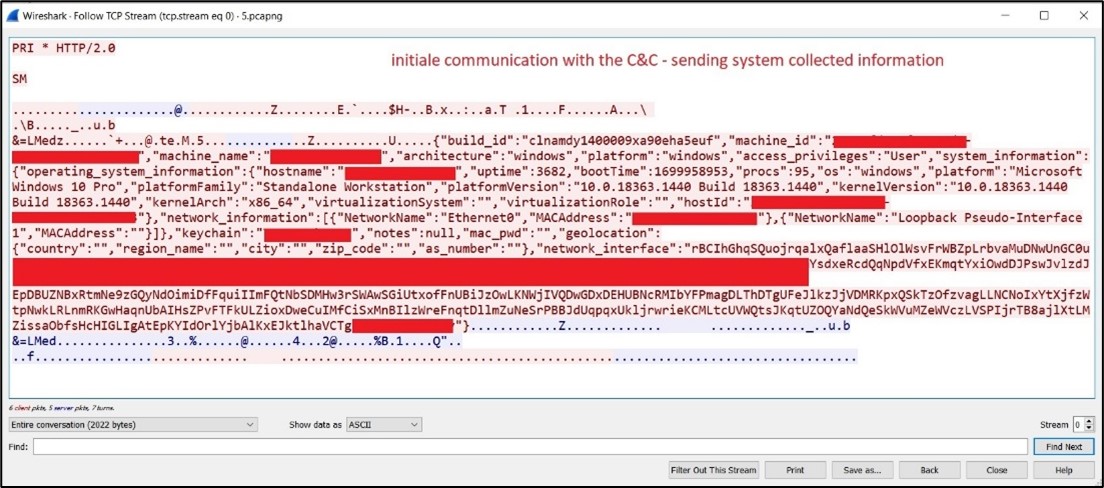
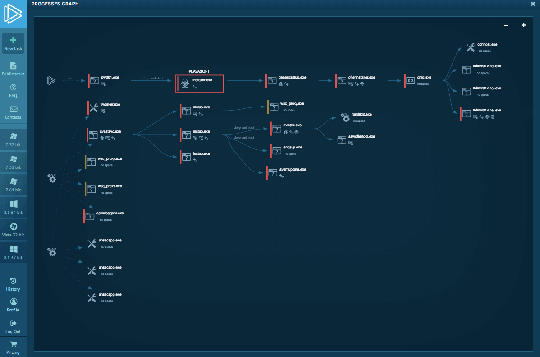
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

TryHackMe Hacktivities

MetaDefender Cloud Advanced threat prevention and detection
Interactive Online Malware Sandbox
de
por adulto (o preço varia de acordo com o tamanho do grupo)