Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware Analysis: Protecting Your Network from Cyber Attacks

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs
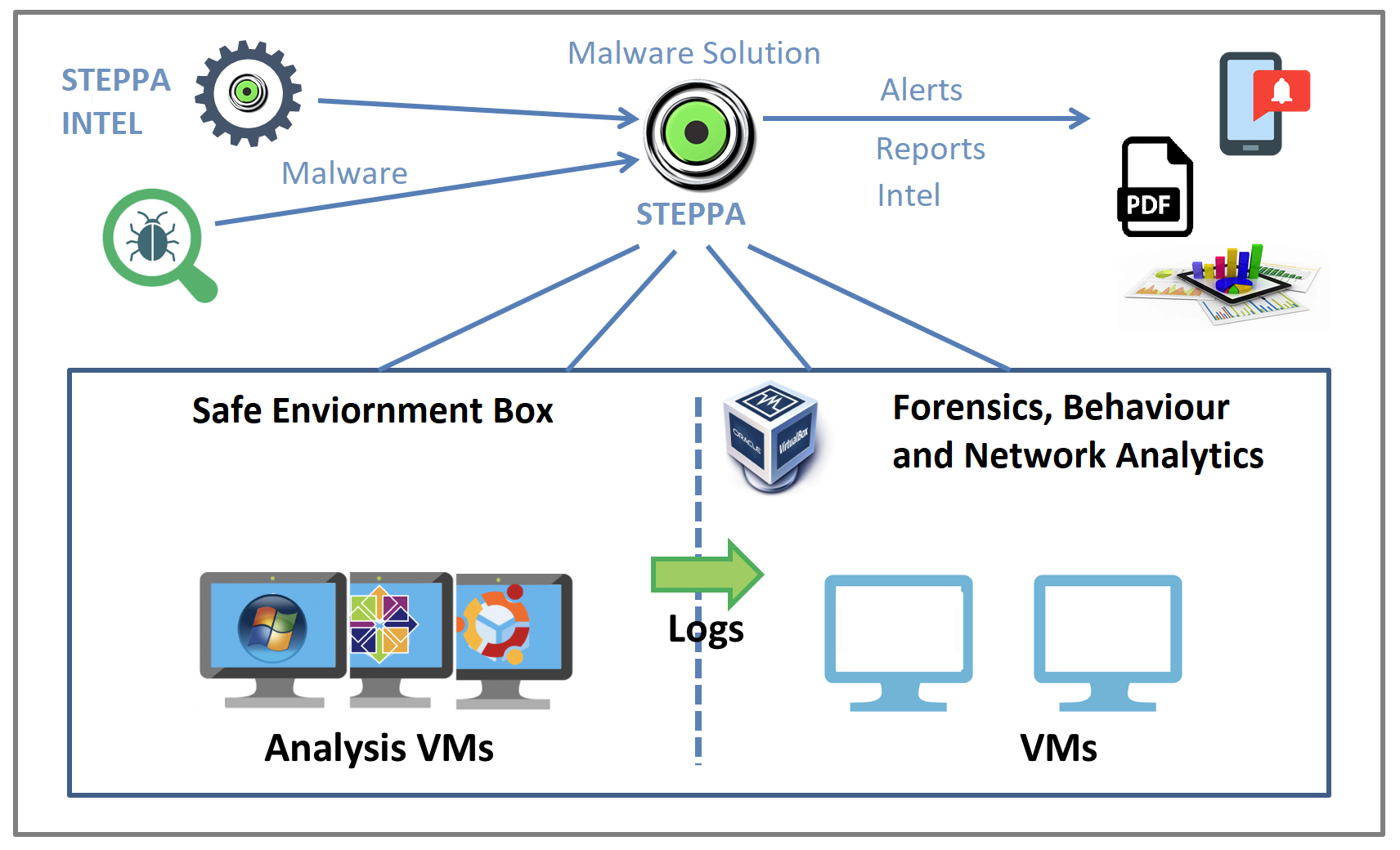
Malware Analysis Solution: Analyze, Detect, and Protect

Detail procedure of malware analysis

Playbook for Malware outbreak

How to build a malware analysis sandbox with Elastic Security

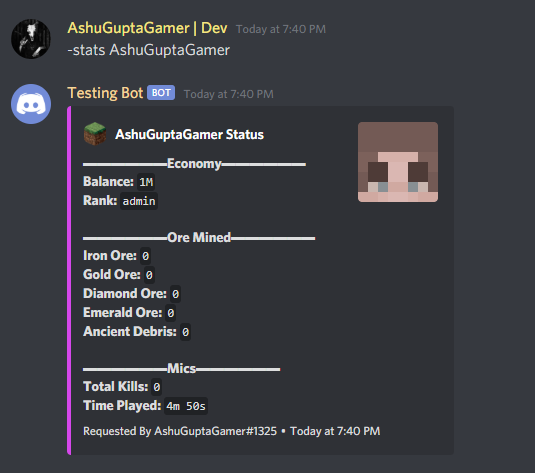
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

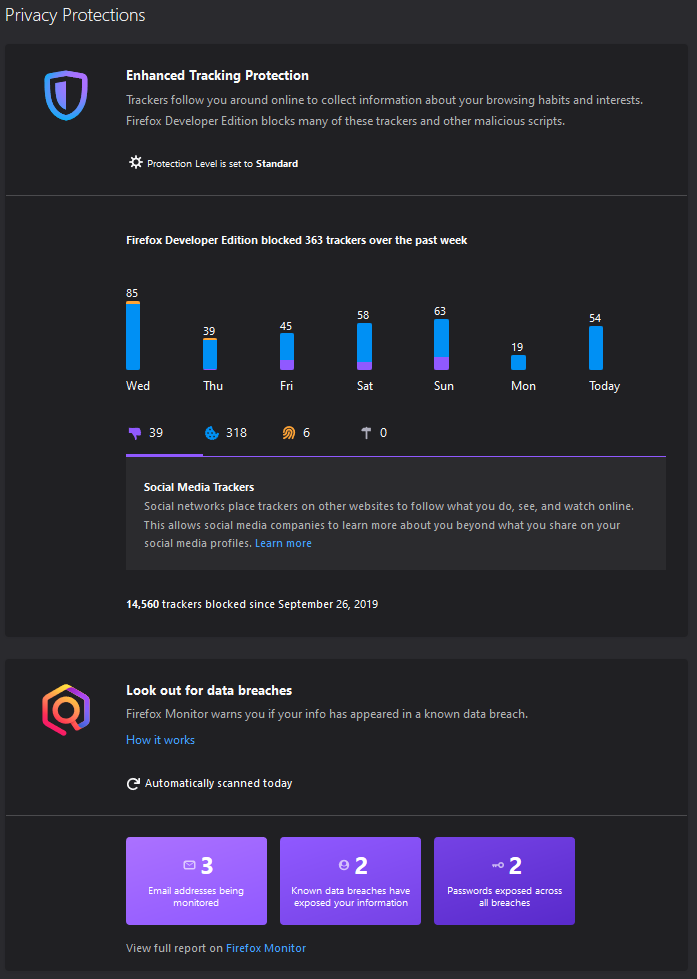
Comprehensive Protection Strategies Against Cyber Threats
Download Free Antivirus Software

Malware analysis index.html Malicious activity

Malware analysis file Malicious activity

Top 10 Types of Information Security Threats for IT Teams

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Malware Analysis: Steps & Examples - CrowdStrike
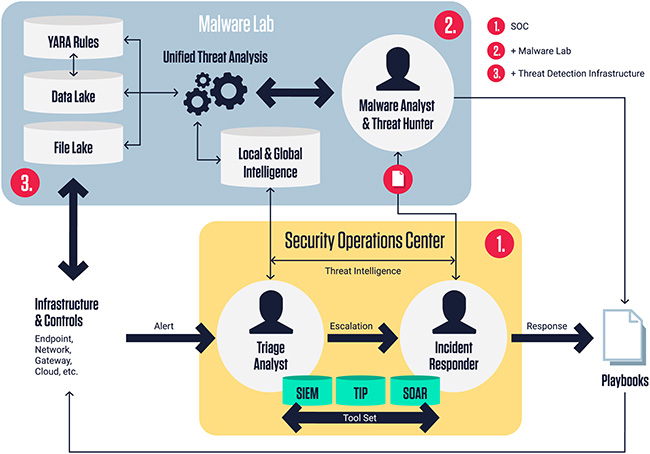
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security
de
por adulto (o preço varia de acordo com o tamanho do grupo)