Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware Analysis Benefits Incident Response

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Info stealers and how to protect against them

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Malware Analysis: Steps & Examples - CrowdStrike

TryHackMe Hacktivities

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

How to build a malware analysis sandbox with Elastic Security

Malware analysis index.html Malicious activity

Malware analysis lockysample.bin.zip Malicious activity

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity
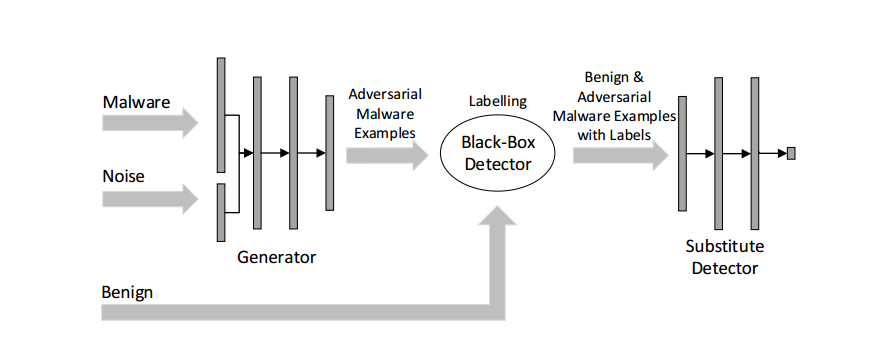
Malware Detection
de
por adulto (o preço varia de acordo com o tamanho do grupo)






